Technology
Beyond Compliance: How We Built a Phishing-Aware Culture Across 1,700 Employees
Compliance checkboxes don't change behaviour. Here's how we used RIOT's AI-powered platform to run real phishing simulations, deliver contextual micro-training via Slack, and cut our vulnerability index by more than half across 1,700 employees.
At lastminute.com, cybersecurity isn’t just a technical matter — it’s a people matter. We operate under PCI-DSS and NIS2 requirements, which means phishing awareness is a compliance obligation with real accountability behind it. But compliance aside, we wanted something that actually changed how 1,700 employees think about the emails landing in their inbox every day. That’s what led us to RIOT.

Where We Started: The Limits of Passive Training
Before adopting a dedicated phishing awareness platform, our security awareness program was built around video-based training: mandatory courses, slides, a quiz at the end. It checked a box, but it had some blind spots. As we had no KPIs to measure effectiveness, we couldn’t tell how many people would click a phishing link, how quickly they’d report a suspicious email, or whether the training was making any real difference. The lack of visibility made continuous improvement difficult. That’s what led us to evaluate a new approach — and ultimately to partner with RIOT.
We needed three things: a phishing simulation platform to test our people in realistic conditions, a training method that actually engaged employees rather than putting them to sleep, and hard data to track whether we were getting better.
Why RIOT: The Albert Difference
Most phishing simulation platforms offer similar functionality — you pick a template, send fake phishing emails, and measure who clicks. RIOT does that too: from their interface, you select the tools and services your organisation actually uses daily, and it generates realistic, customised campaigns based on those. But what tipped the decision for us was Albert.
Albert is RIOT’s AI-powered bot that lives directly in Slack and Google Chat — the tools our people already use every day. When someone falls for a simulated phishing email, Albert reaches out personally, shows the employee the exact email they received, and walks them through what they should have checked to recognise it as a phishing attempt. That immediate, contextual feedback in the moment of failure is far more effective than a training video watched three months earlier.
Beyond incident-specific coaching, Albert delivers 24 micro-training sessions per year — short, interactive “security pills” of 5 to 10 minutes each, spread across the calendar so security stays top of mind without becoming a burden. Employees receive one simulated phishing email per quarter, paired with these regular training nudges, creating a rhythm of continuous learning rather than an annual compliance event.
The Results
Our first phishing campaign was a blind test — no prior warning, no announcement that a simulation program existed. It gave us an honest vulnerability index baseline. From the second campaign onward, we informed employees that simulated phishing was now part of our security program. Combined with Albert’s targeted training, internal communications reminding people to stay alert, and the ongoing micro-training sessions, we saw a steady decline.
Once employees knew that simulated phishing emails could arrive at any time, they began paying closer attention to all incoming messages. This heightened awareness contributed to a broader improvement in overall security posture.
After 12 months, our vulnerability index dropped significantly — less than half of the initial value — representing a real, measurable change in behaviour across 1,700 people.
Keeping It Real: The Challenges
We’d be dishonest if we said everything was seamless. One of our ongoing challenges is training completion rates. Our employees face a significant load of mandatory corporate training across multiple domains — compliance, privacy, HR policies, product knowledge — and security training competes for the same limited attention. For this reason we decided not to push Albert too aggressively to avoid adding to the fatigue.
This is a common reality in large organisations, and there’s no magic fix. What helps is that Albert’s format — short, conversational, embedded in tools people already use — has a lower friction threshold than yet another e-learning platform. The engagement we do get tends to be higher quality because people are interacting, not just clicking “next” to finish a module.
The Partnership Model: Why Support Matters
We don’t have unlimited internal bandwidth to optimise campaign settings, analyse results, and fine-tune the program. That’s why relying on the support of an external provider is essential for us. This includes setup reviews, identifying gaps and suggesting improvements that translate to better KPIs.
This kind of hands-on partnership turns a tool into a managed program, which is critical when your security team is already stretched thin across incident management, compliance, and operational security.
What’s Next: Going Beyond Phishing Simulation
We’ve been running the phishing simulation and Albert training at full speed, and now we’re expanding into other capabilities the same platform offers.
Phishing evaluation button. Since mid-2025, our employees have a button directly in the Gmail interface that leverages an AI engine to evaluate whether a real email they’ve received is a phishing attempt. This puts the power of analysis in the employee’s hands at the exact moment they need it — when they’re staring at a suspicious message and deciding whether to click.
Data breach alerts. We’re rolling out the breach monitoring tool in the coming weeks. It monitors whether employee credentials appear in known data breaches and alerts them directly. Employees can even add their personal email addresses to the monitoring list, extending the protection beyond the corporate perimeter. The system has been running in monitoring mode already, collecting data, and we’ll activate employee-facing alerts shortly.
Security knowledge base. This is one of the features we’re most excited about. We’ve been feeding Albert with our internal policies and procedures, so when someone asks “What software am I authorised to install on my corporate laptop?” or “How do I report a phishing email?” or “What should I do if my laptop is stolen?”, the platform provides accurate answers drawn from our own documentation. It’s turning a training tool into an always-available security assistant.
Looking further ahead: we plan to leverage the creation of custom training modules and deliver them through Albert, starting from any PDF document. This opens the door to packaging our own internal security procedures, policy updates, and lessons learned from real incidents into interactive training — without needing to build an e-learning course from scratch.
What We’d Tell Other Security Teams
If you’re evaluating phishing awareness platforms, here’s what we’ve learned:
Measure before you train. Run a blind baseline campaign before anyone knows the program exists. Without that honest starting point, you’ll never know if you’re improving or just creating a Hawthorne effect.
Interactive beats passive. Video training has its place, but it doesn’t change behaviour the way a contextual, one-on-one coaching moment does. Showing an employee the exact phishing email they just clicked — explaining what the red flags were — creates a learning moment that sticks.
Don’t underestimate the support model. A great platform with poor support becomes another tool you don’t have time to optimise.
Embed security in the tools people already use. Slack and Google Chat are where our people already work. Meeting them there, instead of sending them to yet another portal, makes a measurable difference in engagement.
Think beyond simulation. The real value is in building a security-aware culture where employees have the tools and knowledge to protect themselves — whether that’s a training bot, a phishing evaluation button, breach alerts, or an AI assistant that knows your policies.
Conclusion
At lastminute.com, we believe cybersecurity is a shared responsibility. Our partnership with RIOT is one part of a broader commitment to building a security-first culture across the organisation — one interactive training session, one flagged phishing email, and one policy question at a time.
Read next
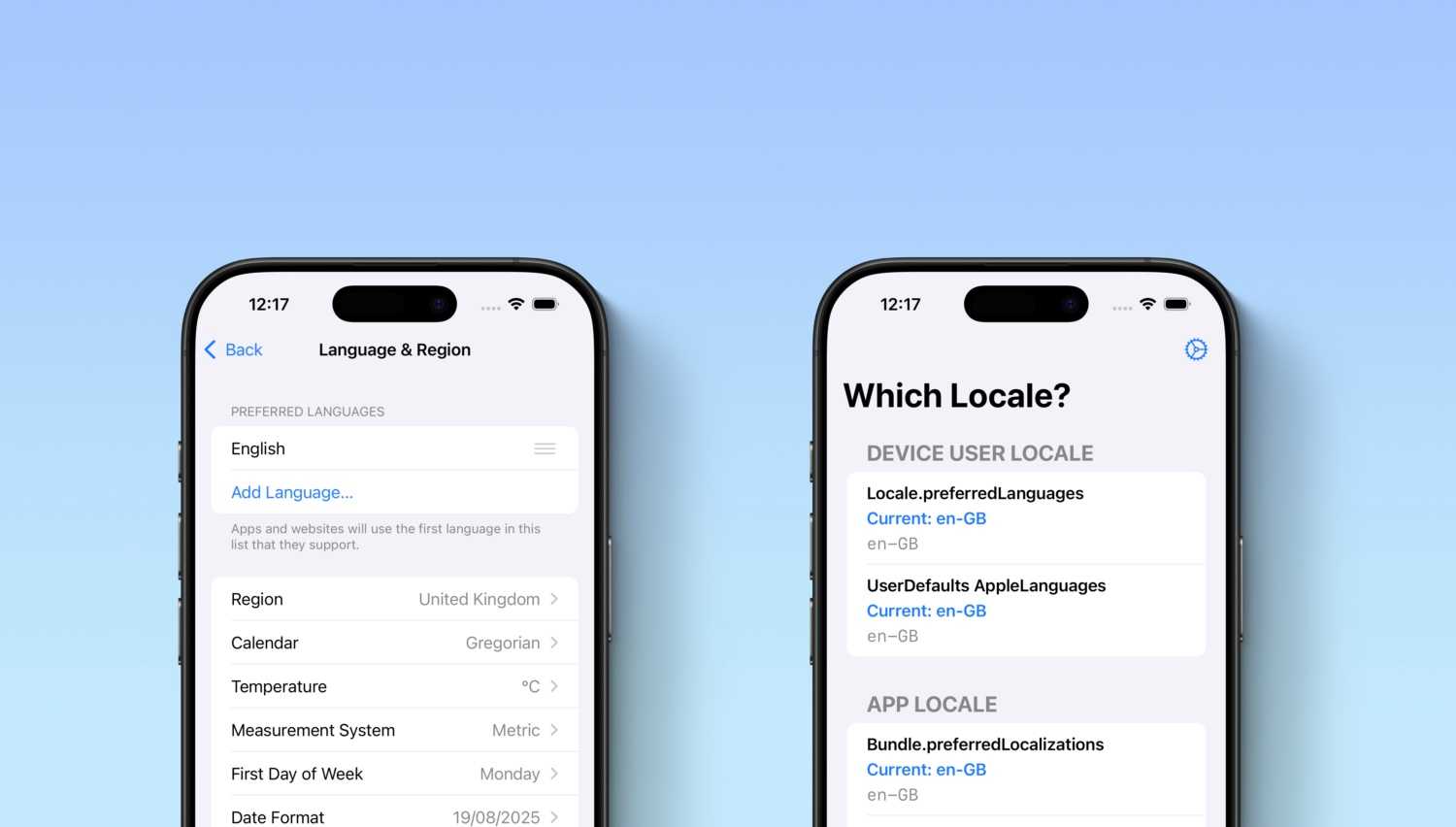
Which Locale? Decoding the Madness Behind iOS Localization and Language Preferences
iOS localization is a wild ride where device and app locales play by their own rules. But don’t worry, after some chaos, Apple’s settings actually matched our expectations. Of course, only after a few twists and turns [...]